In computing, authentication is the process of verifying the identity of a person or device. A common example is entering a username and password when you log in to a website. While a username/password combination is a common way to authenticate your identity, many other types of authentication exist. …
What is authentication and its types?
There are many authentication technologies, ranging from passwords to fingerprints, to confirm the identity of a user before allowing access. Though, it’s often the combination of different types of authentication that provides secure system reinforcement against possible threats.
What is the need of authentication?
Authentication is important because it enables organizations to keep their networks secure by permitting only authenticated users (or processes) to access its protected resources, which may include computer systems, networks, databases, websites and other network-based applications or services.
What is authentication device?
Authentication is the process of identifying and verifying the identity of a system or person in a secure manner. For example, if you log on to a device with a username and password, you are being authenticated as the device is checking that you are really who you say you are.
What are the 3 types of authentication?
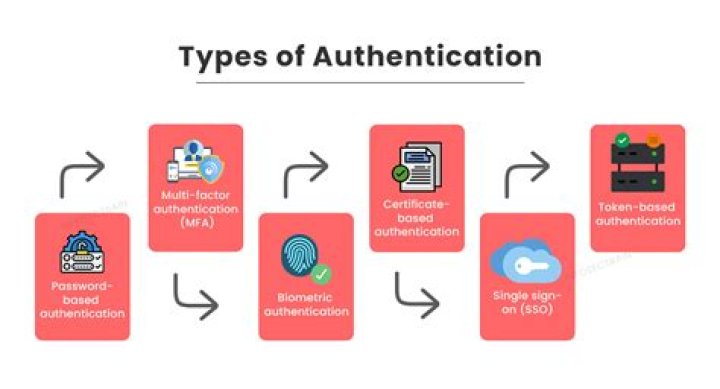
The list below reviews some common authentication methods used to secure modern systems.
- Password-based authentication. Passwords are the most common methods of authentication.
- Multi-factor authentication.
- Certificate-based authentication.
- Biometric authentication.
- Token-based authentication.
How many types of authentication are there?
There are generally three recognized types of authentication factors: Type 1 – Something You Know – includes passwords, PINs, combinations, code words, or secret handshakes. Anything that you can remember and then type, say, do, perform, or otherwise recall when needed falls into this category.
How is authentication done?
In authentication, the user or computer has to prove its identity to the server or client. Usually, authentication by a server entails the use of a user name and password. Other ways to authenticate can be through cards, retina scans, voice recognition, and fingerprints.
Which device is used to authentication of a person?
Biometric devices are authentication devices based on human physical or behavioral traits. Biometrics based on human physical traits generally come in the form of hardware devices like fingerprint readers, iris readers, and palm readers. Biometrics based on behavior traits often come in software form.
What is the most secure authentication method?
What is Beyond Identity? Beyond Identity combines two of the strongest authenticators: biometrics and asymmetric keys. It eliminates the password and provides an extremely secure authentication since the user’s identity is only stored locally on the device and it cannot be moved.
What type of authentication is most secure?
biometric devices
Nowadays, the usage of biometric devices such as hand scanners and retinal scanners is becoming more common in the business environment. It is the most secure method of authentication.Which authentication method is the best?
Our top 5 authentication methods
- Biometric Authentication. Biometric authentication relies on the unique biological traits of a user in order to verify their identity.
- QR Code. QR code authentication is typically used for user authentication and transaction validation.
- SMS OTP.
- Push Notification.
- Behavioral Authentication.
Which authentication is the best?
Top Rated Authentication Products
- Duo / Cisco Secure Access, by Duo. 8.8.
- Google Authenticator. 8.8.
- WatchGuard AuthPoint. 8.7.
- HID DigitalPersona (formerly Crossmatch) 8.2.
What are access control models?
Access control models have four flavors: Mandatory Access Control (MAC), Role-Based Access Control (RBAC), Discretionary Access Control (DAC), and Rule-Based Access Control (RBAC or RB-RBAC). The Mandatory Access Control (or MAC) model gives only the owner and custodian management of the access controls.
What is the main purpose of access control?
The purpose of an access control system is to provide quick, convenient access to those persons who are authorized, while at the same time, restricting access to unauthorized people.
Which multifactor authentication is best?
Top 10 Multi-Factor Authentication (MFA) Software
- Duo Security.
- Google Authenticator.
- LastPass.
- Authy.
- Ping Identity.
- Auth0.
- RSA SecurID® Access.
- OneLogin.
What are the four 4 main access model?
Currently, there are four primary types of access control models: mandatory access control (MAC), role-based access control (RBAC), discretionary access control (DAC), and rule-based access control (RBAC). …
What is access control system how it works?
Access control systems are digital networks that electronically control entry into and out of a designated area. The main elements of an access control system are the tag, tag reader, access control panel, and lock. These work together to create a seamless, automated experience for the user.
In computing, authentication is the process of verifying the identity of a person or device. A common example is entering a username and password when you log in to a website. Entering the correct login information lets the website know 1) who you are and 2) that it is actually you accessing the website.
What is authentication in computing?
Authentication is the process of a user confirming that they are who they say they are on a computer system. In a network, this is often done through inputting a username and password. For networks that require high levels of security, authentication may include other methods.
What are the types of authentication?
What are the types of authentication?
- Single-Factor/Primary Authentication.
- Two-Factor Authentication (2FA)
- Single Sign-On (SSO)
- Multi-Factor Authentication (MFA)
- Password Authentication Protocol (PAP)
- Challenge Handshake Authentication Protocol (CHAP)
- Extensible Authentication Protocol (EAP)
What is authentication in DBMS?
Database authentication is the process or act of confirming that a user who is attempting to log in to a database is authorized to do so, and is only accorded the rights to perform activities that he or she has been authorized to do.
Why is authentication needed?
What are the three types of authentication?
5 Common Authentication Types
- Password-based authentication. Passwords are the most common methods of authentication.
- Multi-factor authentication.
- Certificate-based authentication.
- Biometric authentication.
- Token-based authentication.
What is the purpose of authentication?
Authentication is the process of identifying an individual process or entity that is attempting to log in to a secure domain. Requests for protected resources by unauthenticated users always result in an authentication challenge.
What are the 5 factors of authentication?
Here are the five main authentication factor categories and how they work:
- Knowledge Factors. Knowledge factors require the user to provide some data or information before they can access a secured system.
- Possession Factors.
- Inherence Factors.
- Location Factors.
- Behavior Factors.
What is the best authentication method?
Passwords. One of the most widespread and well-known methods of authentication are passwords.
- Two-Factor Authentication.
- Captcha Test.
- Biometric Authentication.
- Authentication and Machine Learning.
- Public and Private Key-pairs.
- The Bottom Line.
What do you need to know about authentication?
Definition: Authentication is the process of recognizing a user’s identity. It is the mechanism of associating an incoming request with a set of identifying credentials. The credentials provided are compared to those on a file in a database of the authorized user’s information on a local operating system or within an authentication server.
Which is the best definition of mobile authentication?
Mobile authentication — Mobile authentication is the process of verifying user via their devices or verifying the devices themselves. This lets users log into secure locations and resources from anywhere. The mobile authentication process involves multifactor authentication that can include one-time passwords,…
Where does the authentication process take place on a computer?
The process by which access to those resources is restricted to a certain number of users is called access control. The authentication process always comes before the authorization process. User authentication occurs within most human-to-computer interactions outside of guest accounts, automatically logged-in accounts and kiosk computer systems.
When do you use OAuth for pseudo-authentication?
When OAuth is used solely for authentication, it is what is referred to as “pseudo-authentication.” In this approach, the user logs into a system. That system will then request authentication, usually in the form of a token. The user will then forward this request to an authentication server, which will either reject or allow this authentication.